What We Uncover in Real Data Flow Audits: Lessons From the Field
Every data flow audit starts with the same question: Where does your Controlled Unclassified Information (CUI) actually live?
Most organizations have an answer ready. They’ll point to a file server, an ERP system, or a shared drive. And in most cases, those answers are partially correct. The problem is what they’re missing.
Across the data flow audits our team conducts for manufacturers, defense contractors, and other organizations preparing for CMMC, we consistently find CUI in places that leadership didn’t know about, traveling through channels that aren’t documented, and accessible to parties that aren’t accounted for in the compliance boundary.
This post walks through the most common data flow audit findings we encounter and what your organization can learn from them before your own assessment.
Why Organizations Engage Us for Data Flow Audits
The companies that come to us for this work tend to share a few characteristics. They’ve started building their CMMC compliance program but hit a wall when it came to scoping.
They know CUI exists in their environment, but they aren’t confident they’ve identified every system, user, and vendor that touches it. And they recognize that without that clarity, their System Security Plan (SSP) and their entire compliance boundary rest on incomplete information.
Our Security & Risk Assessments include a focused data flow mapping component designed to answer exactly those questions.
We trace how CUI enters the environment, where it’s stored, how it’s transmitted, and where it exits. What we find during that process is remarkably consistent from one engagement to the next.
The Findings That Keep Showing Up
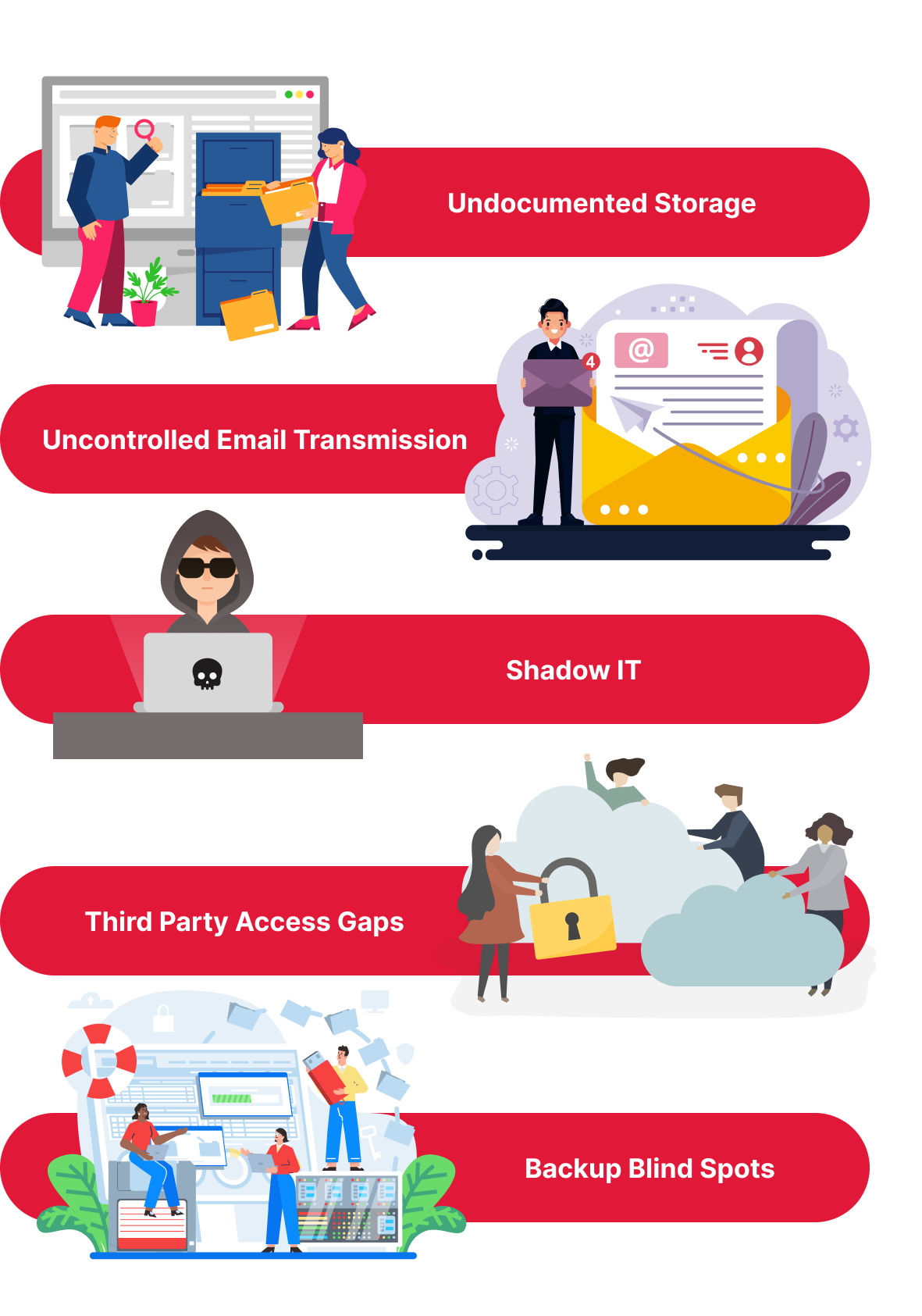
CUI in undocumented storage locations
Organizations typically know about their primary systems, the file servers, databases, and platforms where CUI is supposed to live. What they miss are the secondary and informal locations where CUI ends up over time. We regularly find sensitive data on individual workstations, in personal cloud storage folders, on legacy servers that were never decommissioned, and in project folders that were created outside of IT oversight. None of these locations tend to have the access controls or audit logging that NIST 800-171 requires, and none of them appear in the organization’s data flow diagram.
Email operating as an uncontrolled data transfer channel
CUI moves through email constantly, both internally and with external partners. In most of the environments we assess, email is one of the primary transmission paths for controlled data, yet it’s rarely reflected in the organization’s documented CUI boundary. We see messages containing technical drawings, contract specifications, and controlled reports sent without encryption, without data loss prevention rules, and without documentation that email is a CUI transmission channel. From a compliance standpoint, that’s an entire communication path operating outside the security boundary.
Shadow IT and unsanctioned collaboration tools
This is one of the most common findings across our engagements. Employees use free or personal tier tools to share files with external partners, collaborate on documents, or transfer large files. These tools sit outside IT management, which means no access controls, no logging, and no visibility into what data is passing through them. When that data includes CUI, those tools become part of the compliance boundary whether the organization intended it or not.
Third party access without documentation
Many of the organizations we work with rely on managed IT providers, cloud hosting vendors, or external consultants who have remote access to systems where CUI resides. That access is usually functional and necessary. But in a significant number of our audits, those third party connections aren’t reflected in the data flow diagram, the SSP, or the vendor risk documentation. Under CMMC, third party access to systems handling CUI needs to be scoped and documented. When it isn’t, it’s one of the first things an assessor will flag.
Backup and recovery blind spots
Backups tend to run quietly in the background, and they’re easy to overlook during compliance planning. But a backup containing CUI is still CUI, and the storage destination needs the same protections as the production environment. We frequently find backup data written to network locations with broader access permissions than the source systems, or stored on devices that aren’t included in the organization’s asset inventory. These become uncontrolled CUI repositories that expand the compliance boundary without anyone realizing it.


What Your Organization Can Take From This
These findings aren’t unique to specific industries or company sizes. They surface consistently across the manufacturers, contractors, and service providers we assess.
The common thread is that organizations underestimate how far CUI travels once it enters their environment.
Here’s how to start closing those gaps:
- Treat data flow mapping as your first compliance step, not a later one. If you don’t know where CUI is, your scoping is guesswork and your controls may be protecting the wrong systems.
- Audit the tools your staff actually uses, not just the ones IT manages. Ask employees directly what platforms they use to share files, communicate with partners, and store project data. Shadow IT is one of the fastest ways for CUI to escape your security boundary.
- Document every third party relationship that involves access to CUI bearing systems. This includes managed service providers, cloud hosting vendors, subcontractors, and external consultants. If they can reach your data, they belong in your data flow diagram.
- Review your backup infrastructure. Verify where backup data is stored, who can access it, and whether those storage locations carry the same protections as your production systems.
- Assign ownership and review the map regularly. Data flow documentation should be maintained, not created once and forgotten. Systems change, vendors change, and people change. The map needs to keep up.
What Comes Next

If your organization is preparing for CMMC and you haven’t conducted a formal data flow audit, gaps like these are likely present in your environment. The organizations that find them early are the ones that enter their assessments with confidence rather than uncertainty.
Have questions about your CMMC program? Schedule a time to talk with our team at datasure24.com.
